Craig Condit makes a strong case against JSESSIONID in JSESSIONID considered harmful. And I just learned that it is disabled by default in Grails 1.1.
Category: Code
uHOWTO: Recover stuck modified keys from VMware Player or Workstation
If you use VMware Player or VMware workstation under Linux and you’re an alt-tab fan like me, you might end up with stuck modifier keys, so you can’t use keys like Ctrl, Alt or Shift outside of VMware. Xiao Feng has written a nice script to recover from this annoying condition without having to reboot, and I tought I’d share it with everyone out there:
#!/bin/sh
# Xiao Feng's "Recovering from stuck modifier keys caused by VMware"
# http://bitubique.com/tutorials/recovering-from-stuck-modifier-keys
/usr/bin/xmodmap - << fixme
clear shift
add shift = Shift_L Shift_R
clear lock
add lock = Caps_Lock
clear control
add control = Control_L Control_R
clear mod1
add mod1 = Alt_L Alt_R
clear mod2
add mod2 = Num_Lock
clear mod3
clear mod4
add mod4 = Super_L Super_R
clear mod5
add mod5 = Scroll_Lock
fixme
xset r on
xset m 3.5 4
xset b off
xset s off
update…where id in (select…) and mySQL ERROR 1093
What’s wrong with this picture?
mysql> update ignore flight set intl=1 where id in (select f.id as id from flight f left join airport a on a.id=f.origin where a.country<>'mx' for update);
ERROR 1093 (HY000): You can't specify target table 'flight' for update in FROM clause
This construct is invalid in mySQL
According to the manual,
You can use a subquery for assignment within an UPDATE statement because subqueries are legal in UPDATE and DELETE statements as well as in SELECT statements. However, you cannot use the same table (in this case, table t1) for both the subquery’s FROM clause and the update target.
The equivalent multi-table update does the same and works as intended:
update flight f left join airport a on a.id=f.origin set f.intl=1 where a.country<>'mx';
Bourne Shell Server Pages
Easy. Portable. Buzzword-compliant. Ingenuous. Elegant. Right-out wicked cool: Bourne Shell Server Pages. As I write this I’m looking for a excuse to use this revolutionary technology in my next project!
Behold the simplicity of ASP and the power of sh:
<html>
<body>
<h1><$ echo "Hello, world!" $></h1>
</body>
</html>
Interface21: please take note. I expect a Spring.sh implementation before the year ends. ;-)
[tags]bourneShell, asp, jsp[/tags]
Whitespace Matters
Mark Jason Dominus just released SuperPython 0.91, “a Perl source filter for the SuperPython language, allowing SuperPython code to be embedded into Perl programs”.
In terms of language, it goes way beyond python itself to give proper semantics to whitespace. For instance, here is the Hello World program written in SuperPython:
#!/usr/bin/perl
use SuperPython;
Ain’t it neat? Naturally, the result is
$ ./hello.spy Hello, world.
just as would be expected.
If you want to try this program yourself you might be surprised to find out that copy+paste won’t work, but that’s a small price to pay in exchange or the benefits of the richness of syntax and expresiveness of the language, and anyway you may download the source code for hello.spy right here.
Mark is very optimist in contributing the new features of SuperPython back to python itself, and has kindly offered to work closely with the Python community to see this happen.
Congrats Mark, and keep up the good work!
[tags]code, perl, python, computer languages[/tags]
Moving from MyISAM to InnoDB: bulk table conversion
A couple of years ago Ludovico Magnocavallo tackled the issue of bulk conversion of MySQL tables from MyISAM to InnoDB with an elegant bash snippet.
for t in $(mysql --batch --column-names=false -e "show tables" mydbname); do mysql -e "alter table $t type=InnoDB" mydbname; done
The original post also suggests using grep to limit the scope of the conversion to just a few tables.
(It seems that now Google *does* yield practical answers to this question ;-)
[tags]bash,mysql,innodb[/tags]
md5pass
This snippet is a simple wrapper around Digest::MD5‘s md5_base64() builds unsalted MD5 digests encoded in base64, very useful for LDAP management and LDIF file processing.
#!/usr/bin/perl
++$|;
use Digest::MD5 qw(md5_base64);
if(!defined($pass=shift)) {
print "> ";
$pass=<STDIN>;
chomp $pass;
}
print encrypted($pass)."\n";
sub encrypted {
my($passwd) = @_;
return '{md5}'.md5_base64($passwd).'==';
}
Use it as such:
$ bin/md5pass
> password
{md5}X03MO1qnZdYdgyfeuILPmQ==
[tags]Perl, MD5, code, code snippet[/tags]
Some lovely ASCII Art
Andrew Savige’s Bottles of Beer have been found by the Python pundits (and by some gutless Perl defectors ;-) ) and are being waved as a textbook executable-line-noise example. There’s people that can’t stand beauty when they see it.
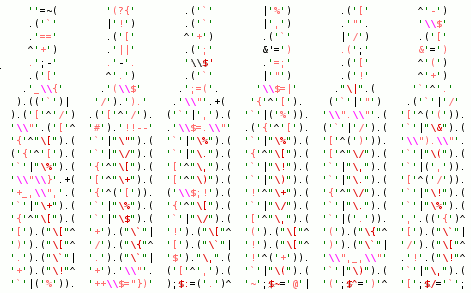
(That code is now an image -see below- but you can always get the original source code).
Yup, it is a Perl program. Yes, it *does* run, with interesting results. There’s even a CPAN module — Acme::EyeDrops — that turns your own Perl programs into purposely unmaintainable yet beautiful works of art that can make the entire Python Party cringe in disgust. You have to admit that there’s certain merit in making grown men cry. Automatically, no less. Go and read how it’s done.
So the Obfuscated Python Contest is incredibly boring. I couldn’t care less.
Via Carlos de la Guardia/Marc Abramowitz/Chris Petrilli.
Update 20060916: Replaced the code with a graphical version because WordPress 2.0 doesn’t play well with the text hightlight plugin.
[tags]Perl, Python, Obfuscation, ASCII art[/tags]
Demo for Luhn algorithm in PHP
If you have a number that adheres to the Luhn algorithm for validation, you may check it easily with this short PHP snippet.
<?php
function luhn($str) {
$odd = !strlen($str)%2;
$sum = 0;
for($i=0;$i<strlen($str);++$i) {
$n=0+$str[$i];
$odd=!$odd;
if($odd) {
$sum+=$n;
} else {
$x=2*$n;
$sum+=$x>9?$x-9:$x;
}
}
return(($sum%10)==0);
}
$num = $_GET['number'];
?>
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN" "http://www.w3.org/TR/html4/strict.dtd">
<html>
<head>
<title>Online Luhn algorithm test</title>
<meta http-equiv="Content-Type" content="text/html; charset=ISO-8859-1">
</head>
<body>
<?php if($num) { ?>
<?php if(luhn($num)) { ?>
<div style="background:#ddffdd;border:1px solid #004400;">
<?=htmlspecialchars($num)?> is valid
</div>
<?php } else { ?>
<div style="background:#ffdddd;border:1px solid #880000;">
<?=htmlspecialchars($num)?> is NOT valid
</div>
<?php } ?>
<?php } ?>
<form action="luhn.php" method="GET">
<div>
Number: <input type="text" name="number" value="<?=urlencode($num)?>" size="40"/>
<input type="button" name="btSend" value="Check"/>
</div>
</form>
</body>
(Download)
You may test this script at https://javier.rodriguez.org.mx/code/luhn-test.php.
Please consider that this is a demo, so please do not use this to check credit card numbers unless you send me an expiry date. CCV2 has taken over as the preferred method for credit card number validation anyway.
Find out LDAP client IPs
ips.pl is a simple perl filter that processes SunONE Directory Server 5.2 access logs to find out the IP addresses that queries are coming from. It’s very useful to evaluate the impact for migrating LDAP infrastructures. Most comments and variable names are in spanish but the code should be clear enough to any SODS sysadmin. Or drop me a line if you absolutely need an all-english version.
#!/usr/bin/perl
# ips.pl $Revision: 1.1 $
# Analiza archivos access de Sun ONE Directory Server 5.2 para generar
# reporte de IPs de clientes y servidores
# Copyright (C) 2005 Javier Arturo Rodriguez
use strict;
my($acceso);
my $filename = shift @ARGV;
die("Usage:\t$0 <filename>\n\tbunzip2 -c <filename.bz2> | $0 -\n") unless $file
name;
open(FILE,"<$filename");
while(<FILE>) {
chomp;
if($_=~m,^\[(.*?)\].*?connection from ([\d\.]+) to ([\d\.]+),) {
$acceso->{$3}->{$2}->{TS}=$1;
++$acceso->{$3}->{$2}->{CNT};
}
}
close(FILE);
foreach my $dst (sort keys %{$acceso||{}}) {
print "Acceden a traves de $dst\n";
foreach my $src (
reverse sort { $acceso->{$dst}->{$a}->{CNT} <=> $acceso->{$dst}
->{$b}->{CNT} }
keys %{$acceso->{$dst}||{}}
) {
printf(" %-15s (last seen on %s; %d hit%s)\n",
$src,
$acceso->{$dst}->{$src}->{TS},
$acceso->{$dst}->{$src}->{CNT},
$acceso->{$dst}->{$src}->{CNT}==1?'':'s',
);
}
}
(Download)